
Scammers are impersonating security researchers to sell fraudulent proof-of-concept ProxyNotShell exploits for recently discovered Microsoft Exchange zero-day flaws. Last week, Vietnamese cyber security firm GTSC said that some of their clients had been attacked using two new zero-day flaws in Microsoft Exchange.
The researchers revealed the flaws with Trend Micro’s Zero Day Initiative, and Microsoft verified that they were being used in attacks, indicating that they would deliver security updates more rapidly.
“Microsoft observed these attacks in fewer than ten organizations globally. MSTIC assesses with medium confidence that the single activity group is likely to be a state-sponsored organization,” Microsoft shared in an analysis of the attacks.
Security researchers are keeping the technical specifics of the flaws secret, and it appears that just a few threat actors are taking advantage of them. As a result, other experts and attackers wait for the vulnerabilities to be public before utilizing them in their activities, whether defending a network or breaching one.
Cybercriminals selling fake exploits
To take advantage of this lull in the storm, a scammer has begun creating GitHub repositories where they attempt to sell fake proof-of-concept exploits for the Exchange CVE-2022-41040 and CVE-2022-41082 vulnerabilities.
John Hammond of the Huntress Lab has been monitoring these frauds, and he’s discovered five new accounts attempting to sell fraudulent exploits. The usernames ‘jml4da,’ ‘TimWallbey,’ ‘Liu Zhao Khin (0daylabin)’, ‘R007er,’ and ‘spher0x’ were used by these accounts.
After learning that the account was a scam, Paulo Pacheco discovered that it had been impersonating Kevin Beaumont (aka GossTheDog), a prominent security researcher/professional who has published findings on the newest Exchange flaws and mitigation strategies.
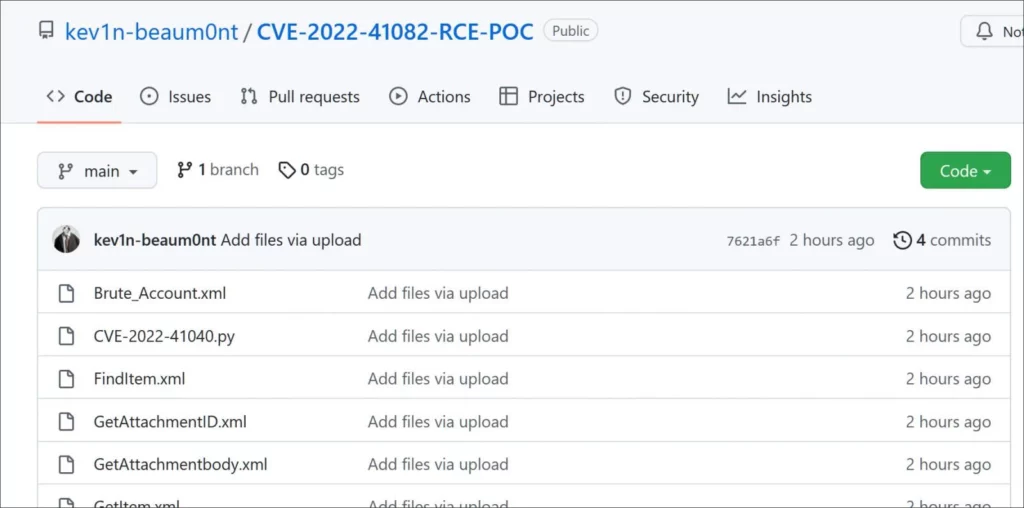
The repositories are empty of any vital information. Still, the README.md explains what is presently known about the new flaws, followed by a sales pitch for one copy of a PoC exploit for the zero days.
“This means it can go unnoticed by the user and potentially by the security team. Such a powerful tool should not be fully public; there is strictly only one copy available so that a REAL researcher can use it: https://satoshidisk.com/pay/xxx,” reads the text in the scam repository.
The README files contain a link to a SatoshiDisk page where the impostor is attempting to sell you a counterfeit exploit for 0.01825265 Bitcoin, worth roughly $420.
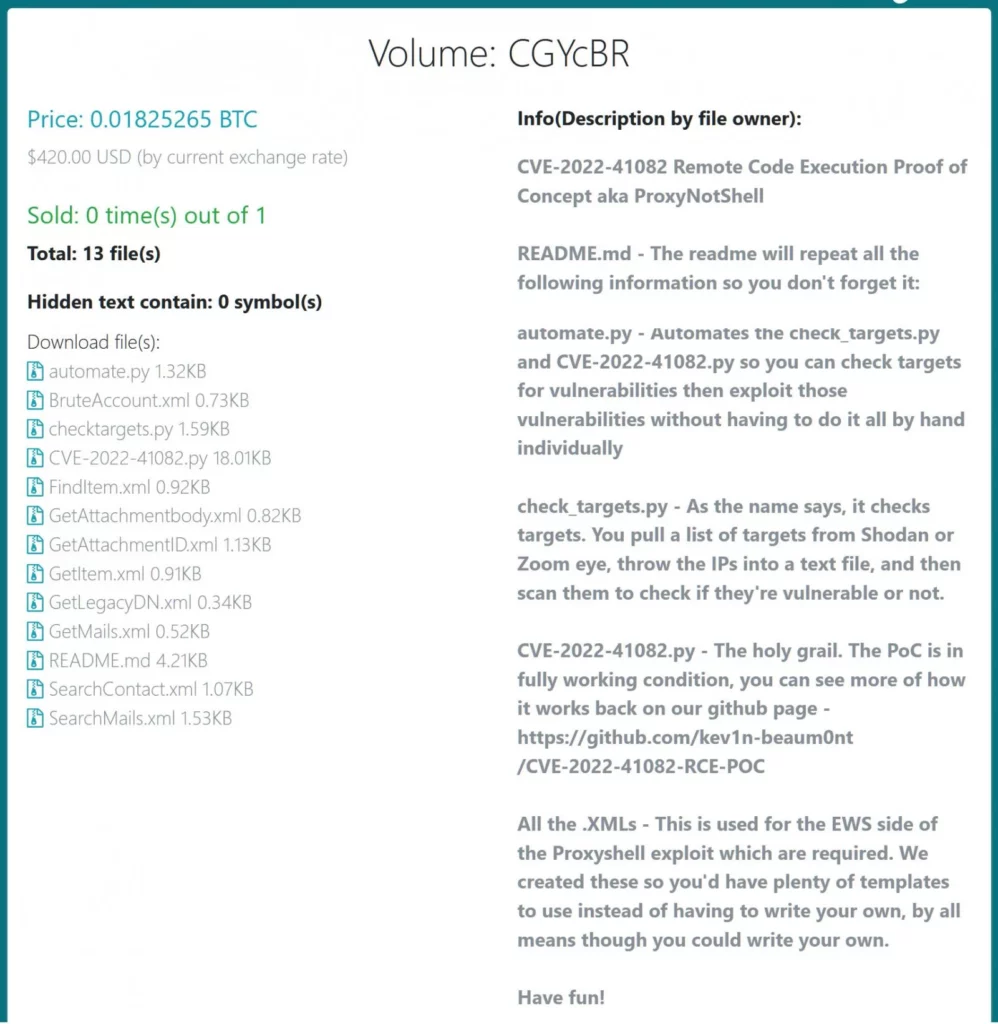
It’s clear that these holes are far more valuable than $400, and Zerodium is willing to pay at least $250,000 for Microsoft Exchange remote code execution zero-day vulnerabilities. It should go without saying that sending any bitcoin will not result in you receiving anything.
Furthermore, with all the data presently accessible, finding a vulnerability in the bugs is likely not difficult for more advanced threat actors like state-sponsored hackers that would be incentivized to breach organizations of interest.





